Our Process
A Digital Forensic Examiner is your new era “Sherlock Holmes”. Our investigations follow the rigorous NIST-recommended four-stage process providing analysis results in reports for personal use and courtroom.
The Four Phases of Digital Forensics

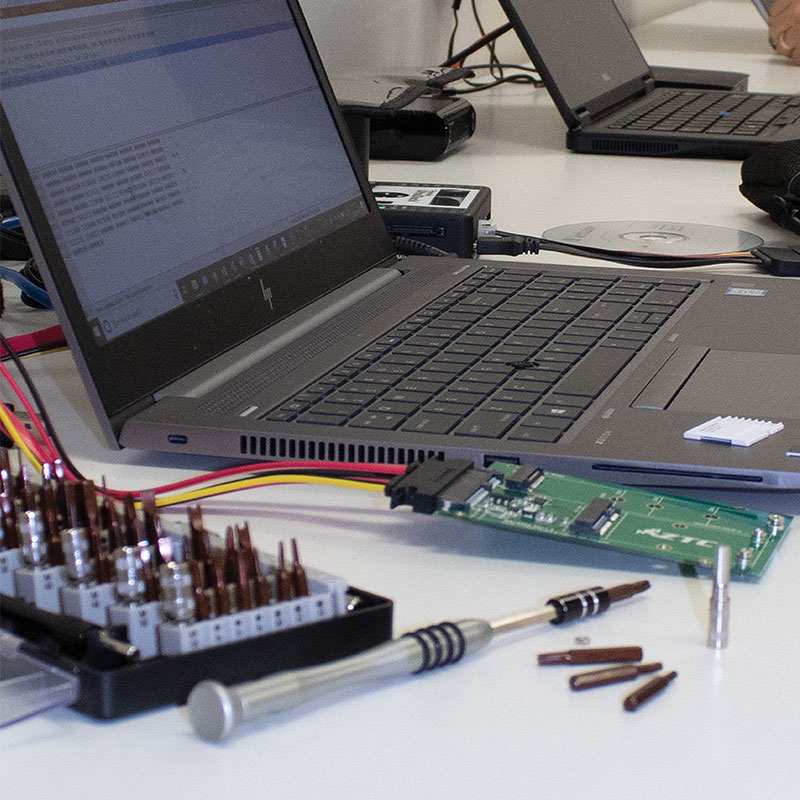
Collection
Forensically sound data collection refers to the process by which data is collected for discovery without any changes to the original evidence or the metadata
To be forensically sound, a data collection process must be defensible in court, repeatable and well documented.
- Deadbox imaging – When you "pull the plug" on the computer system prior to acquiring an exact copy of the hard drive.
- Live imaging – An image of RAM (memory) can also be captured, providing you with a complete picture of how the operating system has been used immediately prior to the imaging process.
- Bypass hard drive encryption (if enabled)
- Information stored in memory can be accessed until you turn the computer off. Once you shut down a computer any information stored in the computer memory is lost.
Examination
The process of uploading the newly acquired image and all the data that was acquired using forensics software to help separate all the data to better analyze. Information such as documents, database information, pictures, internet search history, emails, dates, and times, operating system / file system information, etc.

Analysis
Forensic data analysis is the in-depth analysis and examination of the Electronically Stored Information (ESI), with the purpose of identifying information that may support or contest matters in a civil or criminal investigation or court proceeding.

Reporting
Digital forensics examiners must report and present findings on a very technical discipline in a simplistic manner. That may be to a supervisor, client, attorney, etc. Or even a judge and jury who will read and interpret your report after it has been cross examined.
- Examination log – detailed step-by-step procedures and findings along the way.
- Derivative reports – tool reports, Word / Excel reports that were developed during the examination.
- Final report – to consist of the overview of the case, original forensic request, details of the examination, summary of results and final examiner findings.